Spotify’s 2025 security breach taught every data team one uncomfortable lesson: sometimes your data gets you in trouble and not user credentials.
What happened is that there was a large-scale scraping of music metadata and audio files, along with attackers testing stolen credentials against user accounts.
And this is exactly how most modern data security breaches happen.
Server hacking or breaking firewalls has now become too predictable for cybersecurity teams and too boring for attackers.
| That is why, while most companies lock down their infrastructure and clean their IAM policies, they forget to answer three simple questions: 1. Where is our sensitive data? 2. Who can access it? 3. How secure is that access right now? |
The uncertainty is the real risk, and it’s the reason why organizations are forced to rethink how they can protect their data using Data Security Posture Management.
What is Data Security Posture Management (DSPM)?
DSPM is a ‘data-first’ security discipline that helps companies constantly understand where their data resides, who has access to it, and how safe the access and the data itself is.
Many organizations think that their data is automatically safe because systems are configured correctly. The goal of Data Security Posture Management is to remove that assumption and instead check the data directly.
It discovers data across cloud platforms, SaaS tools, warehouses, analytic softwares, etc and then classifies it based on its business value, sensitivity, and regulatory relevance.
After that, DSPM maps access paths, usage patterns, and exposure points so teams can see how the data is getting used.
| Must-know fact: The most powerful ability of DSPM is that it can dig up unexpected data behavior. You may think your data got breached suddenly, but in most scenarios, the leak starts happening way back. Therefore, you should never ignore signs like an unusual increase in query volume, a service account pulling far more records than usual, or a sudden spike in data access. |

Moreover, as founders now are increasingly relying on AI in data management to automate pipelines, power analytics, and train models, making data usage faster and far less predictable, the continuous monitoring of data becomes non-negotiable.
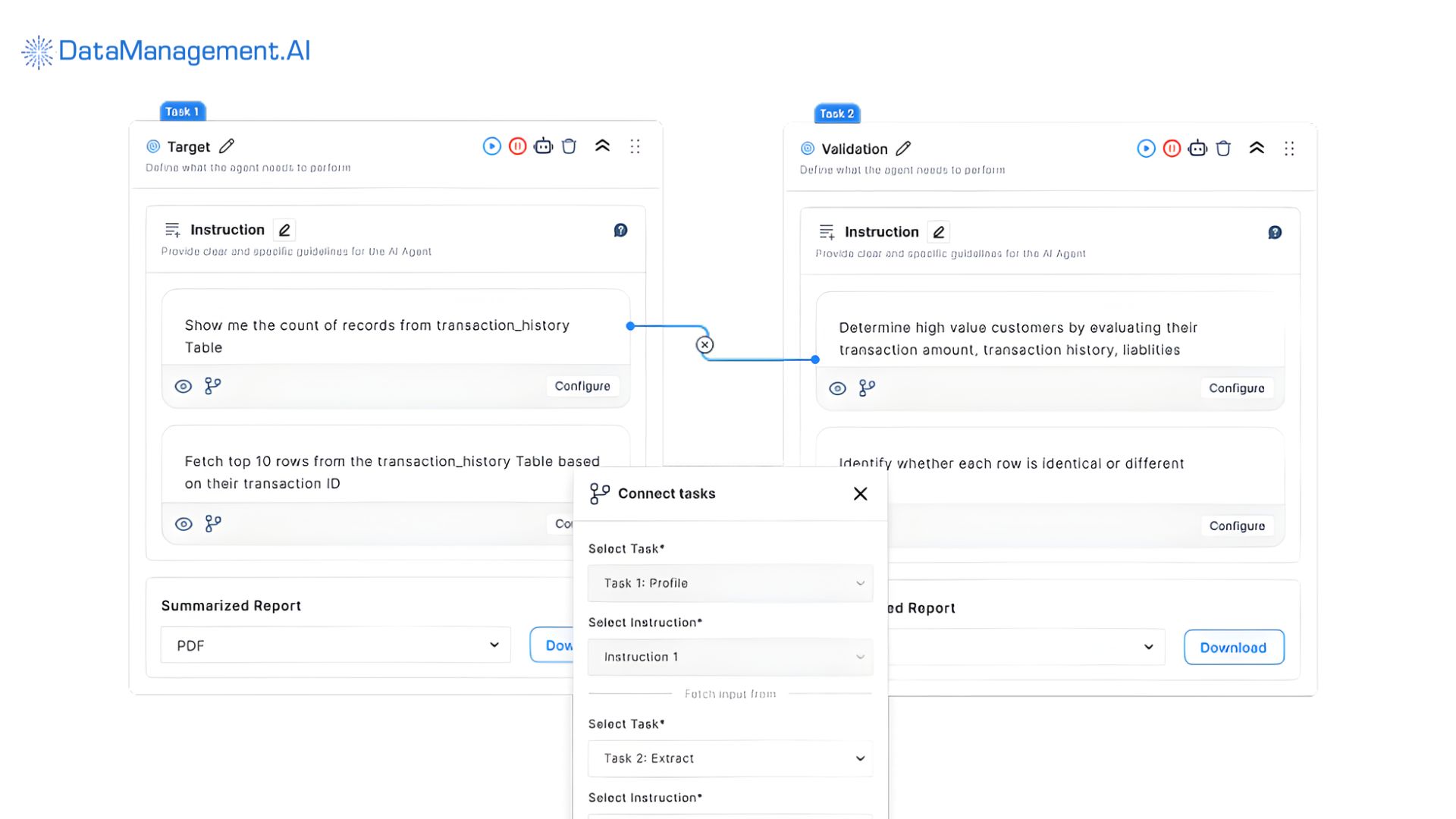
This is where DataManagement.AI steps in and extends DSPM beyond static visibility.
By layering its operational anomaly detection feature on data posture insights, your team can automatically spot unusual patterns or outliers in key metrics like access frequency, data movement or error rates.
Therefore, after plugging in DataManagement.AI to your existing ERP or PLM, you get the opportunity to take action before the damage is done.
Why does DSPM matter in cloud-first and AI-driven enterprises?
Cloud-first architecture’s ability to deliver speed and flexibility and AI’s promise to provide smarter decisions have completely changed how data is created, stored, copied, and consumed. The whole process is often too fast for security teams to keep up.
There are three main ways:
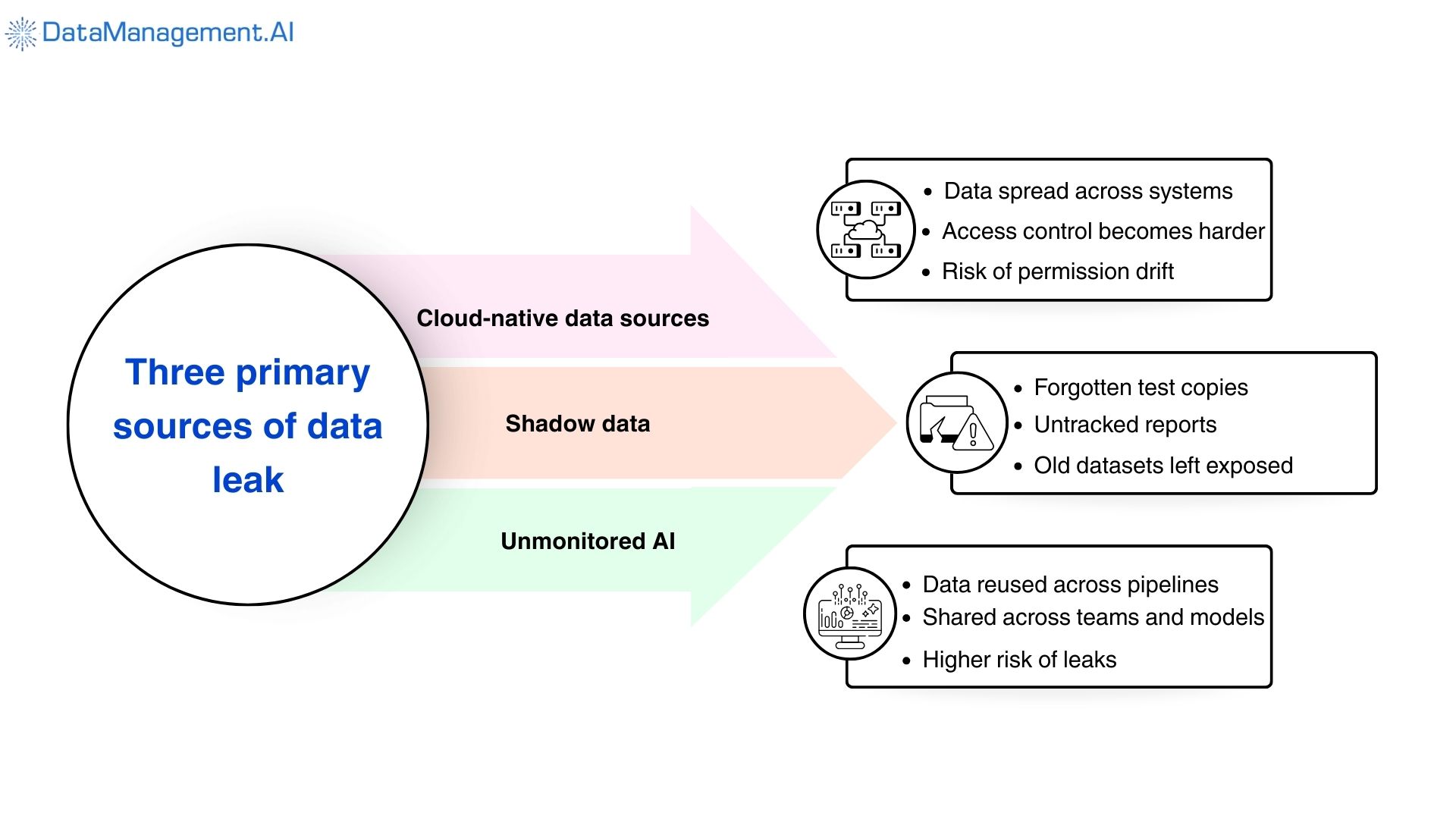
- First, there’s an explosion of cloud-native data stores. Thus, sensitive data is now present across warehouses, data lakes, object storage, SaaS platforms, backups, and replicas, increasing the chance of areas where control over access can drift.
Data Security Posture Management continuously discovers these data stores, even if it was created an hour ago, and identifies which ones contain sensitive data. Earlier, this was done using static inventories or manual tagging, which was slow and led to delayed outcomes.
- Then there’s the issue of shadow data. Before deploying a product, teams make data copies for testing, analytics, or exports, and over time, they forget that these copies even exist. Thus, even if they store sensitive information, they stay unprotected.
DSPM tracks down these files by detecting duplicates, unmanaged data sets, and abandoned data assets. It also shows who accesses these forgotten copies, helping teams eliminate unnecessary exposure.
- Lastly, unmonitored AI accelerates these problems.
Data pulled from different sources for AI pipelines often gets transformed and reused by different teams and models, which exposes it to the risk of being accessed by unauthorized members and leaks.
Implementing Data Security Posture Management can bring this situation under control, as the software will now track if the flow of the data aligns with company policies, removing chances of oversight.
How does Data Security Posture Management work?
Implementing DSPM simply means shifting from periodic checks to a living security model that adapts as your data changes.
Here’s how it works, step by step.
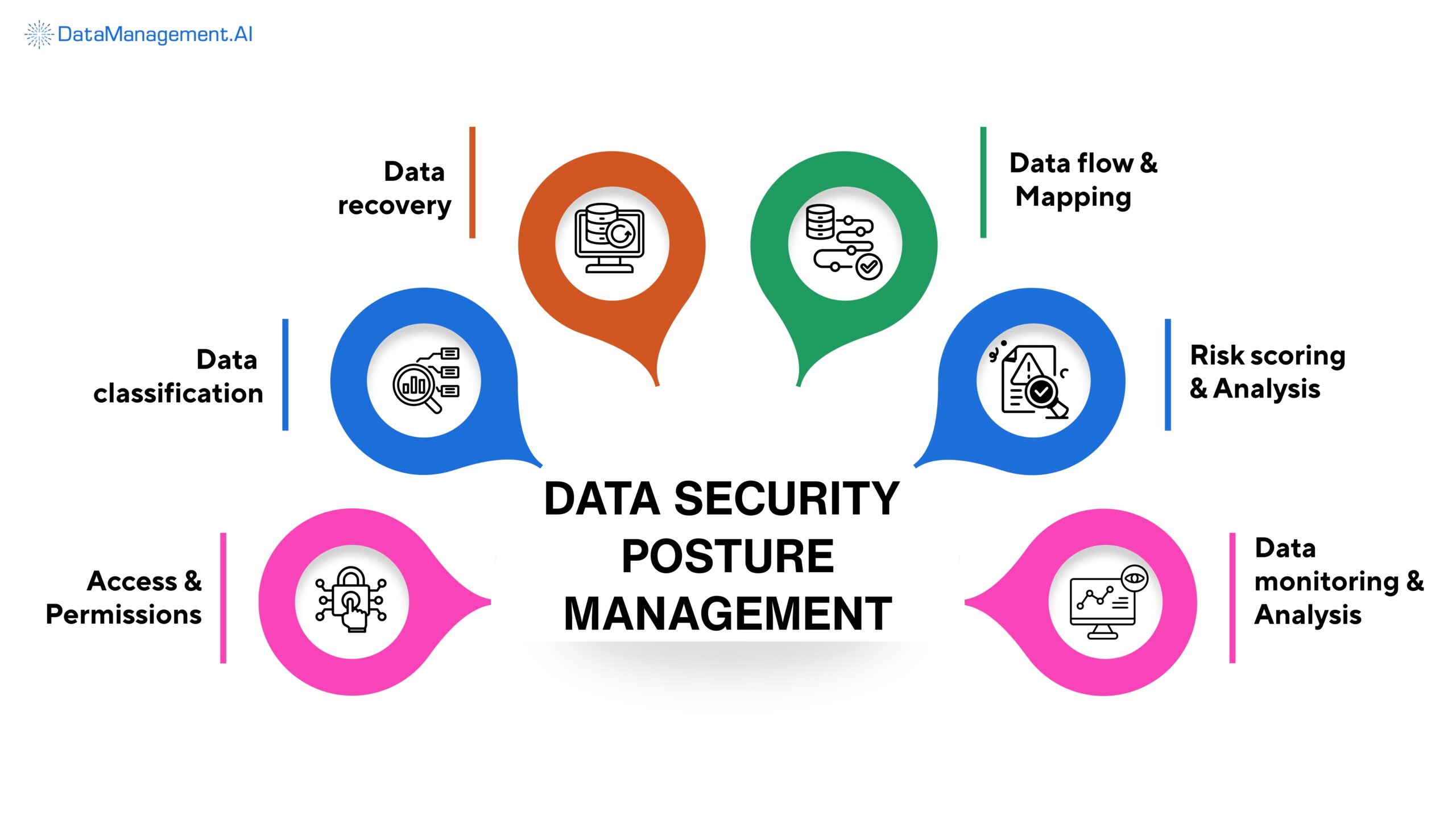
Sensitive data recovery
DSPM doesn’t rely on predefined locations or manual inventories. It programmatically connects to data sources and checks data patterns directly.
This process surfaces sensitive data hidden in unexpected places like temporary cloud buckets, archived tables, application logs, or staging areas that feed AI pipelines.
Data classification and context
After discovery, DSPM applies classification models to identify PII, PHI, PCI, intellectual property, and AI training data.
Moreover, it also tags business and regulatory context on top of this data.
Access, permissions, and identity mapping
Next, instead of just listing permissions in isolation, Data Security Posture Management solutions analyzes effective access.
It correlates identities, inherited roles, service accounts, and machine identities to show who can reach sensitive data. It helps weed out privilege creep, orphaned access, and unwanted bots.
Data flow and lineage mapping
DSPM also reconstructs how data moves through systems over time by connecting directly to your existing data ecosystem.
DataManagement.AI provides you a unified view across all your data sources and destinations, starting from cloud warehouses and storage to analytics platforms and AI pipelines.
It tracks when sensitive data is copied, transformed, exported, or reused downstream, making it easy to see how exposure multiplies as data travels.

Risk scoring and exposure analysis
Data Security Posture Management evaluates risk by combining several factors, such as accessibility, environment, and missing safeguards.
Thus, it doesn’t treat all findings equally; it ranks exposures based on their real-world impact, which helps teams act decisively.
Continuous monitoring and alerting
Lastly, DSPM acts as a watchdog for your sensitive data. Every time a new dataset appears, permissions drift, unusual access patterns emerge, or new risks are detected, it triggers alerts in real time.
Thus, it is a great assistant for security teams.
Data Security Posture Management best practices
Most organizations struggle with DSPM not because the technology is complex, but because they treat it like just another security control.
However, it works best when it’s approached as a visibility and prioritization layer first.
Here are some of the DSPM best practices that everyone should adopt:
Start with visibility – not controls
Before you start locking anything down, focus on understanding where your sensitive data is and how it’s used. Premature controls often break workflows without reducing risks.
Thus, DSPM should first give teams a clear picture of the data landscape, including unknown datasets and hidden access paths.
Prioritize only high-risk data
Not every dataset deserves the same level of attention. DSPM is most effective when it’s used to surface the small percentage of data that carries the highest impact if exposed.
Reducing risks in a few critical areas often delivers more value than months of low-impact cleanups.
Tie DSPM insights to remediation workflows
Visibility alone will be of no help if solutions don’t follow.
Thus, DSPM findings should flow directly into remediation processes (the steps teams take to reduce exposure). This can include tightening or revoking excess permissions, encrypting sensitive datasets, isolating data from non-essential systems, etc.
The faster these insights turn into action, the more effectively DSPM reduces actual risk.
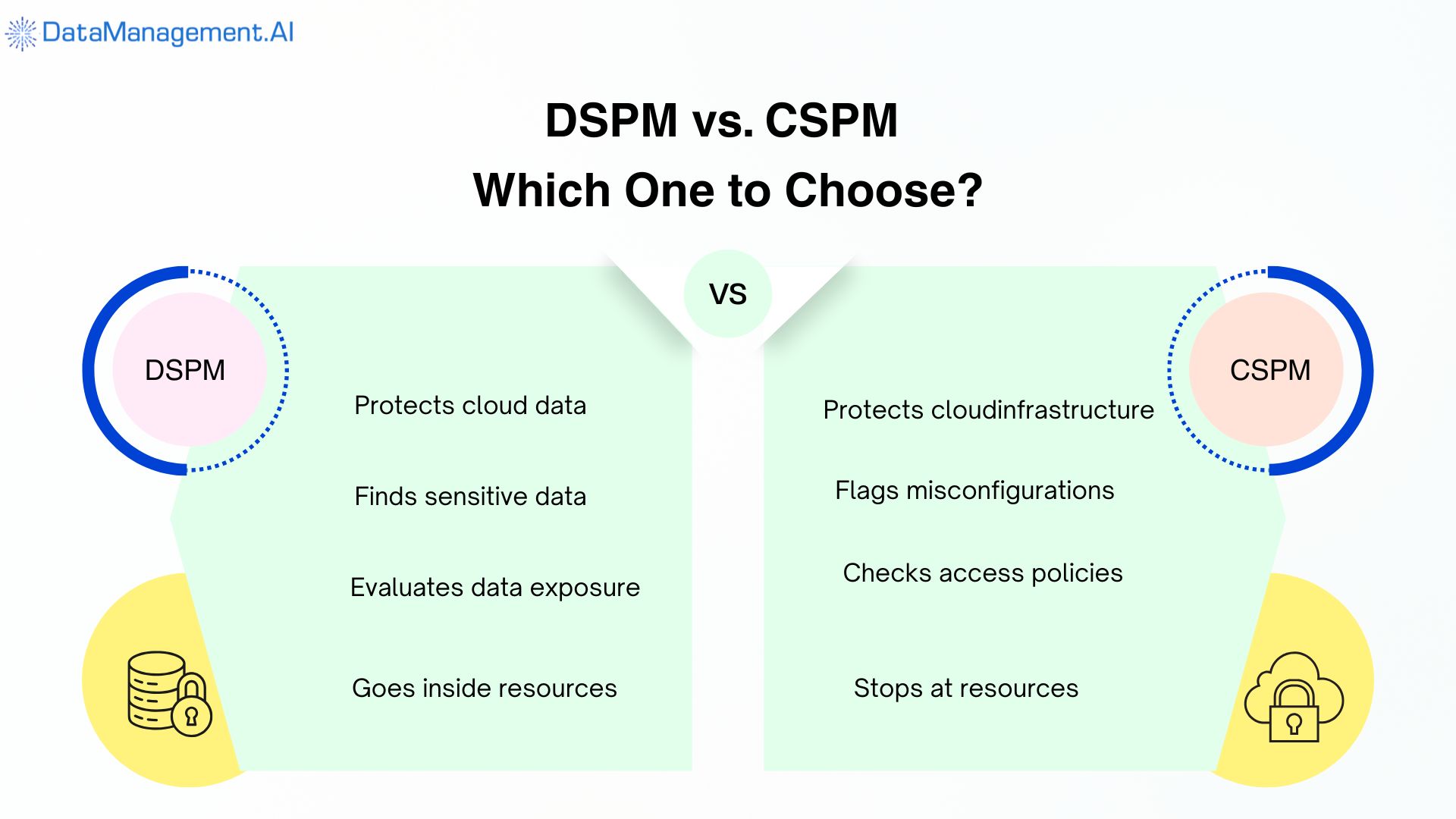
At this point, a question arises: Isn’t this already covered by Cloud Security Posture Management or CSPM?
Not quite.
CSPM focuses on the security posture of cloud infrastructure. It tells you whether resources are misconfigured, storage is public, or policies deviate from best practices. That’s valuable, but it stops at the infrastructure layer.
DSPM operates one level deeper. It focuses on the data inside those cloud resources.
Two storage buckets may look identical from a CSPM perspective, yet one might contain public marketing assets while the other holds sensitive customer records. DSPM makes that distinction first and then evaluates risk.
In modern and advanced environments, infrastructure can be perfectly configured while data exposure still exists. DSPM closes that gap.
That’s why it’s not Data Security Posture Management vs Cloud Security Posture Management. DSPM works with CSPM when protecting what matters most.
If putting all of these processes into motion feels overwhelming, you’re not alone.
This is exactly what DataManagement.AI simplifies. By integrating directly with your existing data ecosystem, it brings visibility, risk prioritization, and remediation signals together in one place without forcing teams to re-architect their workflows.
If you’d like to see how this works in practice, you can schedule a call with us to explore a live demo and understand how our platform supports DSPM in real-world environments.
Quick-action DSPM readiness checklist
Use this quick checklist to assess how prepared your organization really is for Data Security Posture Management.
If you hesitate on more than one of these, DSPM should be a priority.
Do you know where sensitive data lives?
Not just primary databases, but backups, exports, analytics tables, and temporary datasets created across teams and tools.
Can you trace access paths?
This includes human users, service accounts, automated jobs, and AI agents, and whether that access is intentional or simply inherited over time.
Can you prove compliance?
Beyond policies and documentation, can you demonstrate where regulated data exists, who can access it, and how it’s protected right now?
Can you secure AI data pipelines?
From training data ingestion to model outputs, do you have visibility into how sensitive data flows through AI and analytics workflows?
If any of these answers are unclear, get in touch with us. Schedule a demo call now!



